The Microsoft 365 environment ranks among the primary platforms targeted by threat actors. By its very nature, it is exposed to a wide spectrum of offensive operations — and precisely for this reason, Microsoft continuously introduces new tools and configurations to help organizations cope with this ever-shifting landscape of attacks (such as Conditional Access policies and security-focused updates).
Among the various attack types observed in the wild, Password-Spray Attacks stand out as one that organizations must build an effective defense against. Identifying and verifying whether your environment is being targeted by this kind of operation is, in fact, relatively straightforward.
On December 27, 2024, Fortgale detected an offensive campaign of notable interest and scale. It consists of a large-scale Microsoft 365 user enumeration operation, directed at Italian and European companies by a threat actor — likely an organized group — internally tracked as Mater Nebula (Mater-N).
How to defend yourself and find out if you’re affected?

Before diving into the technical details of the attack, we want to share some practical guidance on the most effective strategies to limit your exposure to this type of threat:
- Enable MFA for all Microsoft 365 users
- Enforce strong password policies (leverage Intune Policies)
- Disable legacy protocols (often still active for backward compatibility)
- Monitor for suspicious activity
- Identify suspicious User-Agents
For further support or inquiries, get in touch with us.
Campaign Details: Operation MN-1224
The malicious campaign was launched on December 27, 2024, from numerous IPv6 addresses belonging to the ISP Netassist. The activity consists of user enumeration and password spraying operations carried out through the o365enum tool.
By correlating these indicators, Fortgale was able to isolate the suspicious activity and confirm its presence across multiple tenants protected by our MDR service.
The attacker’s objectives
We assess with high confidence that this offensive campaign was primarily designed to map Microsoft 365 accounts and subsequently follow up with additional offensive operations, specifically Phishing attacks.
As previously highlighted in our analysis of the Supercar Phishing Kit Targeting Microsoft 365, attackers can easily bypass MFA and gain access to victims’ email inboxes.
As a result, organizations are exposed to the following risks:
- Account compromise through Password Spraying
- Account compromise through follow-on Phishing activity
- Targeted Phishing campaigns directed at their users
- Abuse of their email accounts to launch Phishing campaigns against third parties
The offensive activity
The enumeration campaign appears to have been launched in the final days of December 2024 (December 27) and, as previously noted, originates from numerous systems belonging to the ISP Netassist.
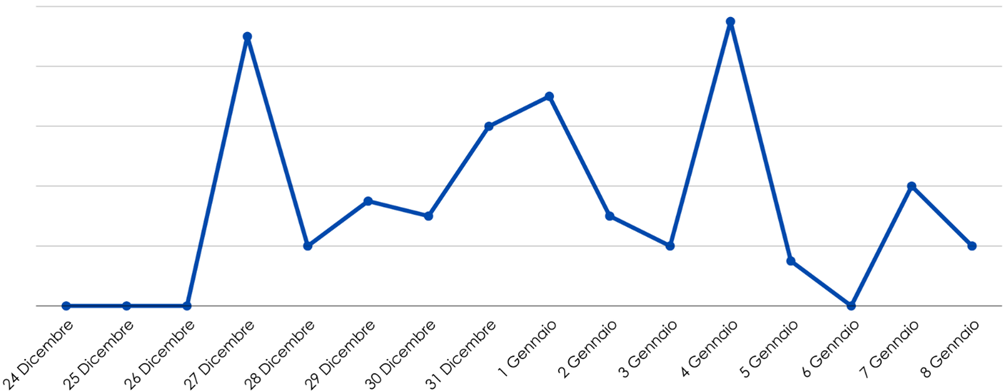
A notable finding is the presence of activity spikes recorded on December 27 and January 4, interspersed with days of significantly lower request volume. This distribution suggests a deliberate scanning strategy, alternating between bursts of activity and periods of reduced operations — likely designed to evade detection mechanisms or avoid overloading target infrastructure.
We assess this to be a large-scale attack leveraging email addresses sourced from previously known compromises (combolists). The nature of the activity, its sheer scale, and the absence of subsequent login attempts all point to a primary objective: building validated lists of active accounts for use in future, far more targeted attacks.
The activity remains ongoing as of January 9, 2025, and may continue for an extended period, carrying the risk of further enumeration waves or unauthorized access attempts. The following chart illustrates the activity trend over the analyzed timeframe:
Lo strumento utilizzato
o365enum is an open-source tool available on GitHub (repo: gremwell/o365enum), designed to perform enumeration of Microsoft Office 365 accounts.
By leveraging response mechanisms from Microsoft’s public APIs, it is used to determine whether specific accounts exist within an organization. This process — known as user enumeration — represents the critical first step in the kill chain leading to further cyberattacks.
Its enumeration technique relies on sending requests to Microsoft’s public APIs and analyzing the responses — such as specific error codes or confirmation messages — to determine whether a given email address is associated with an active account. The tool supports target lists, either as predefined email addresses or common name patterns, generating requests iteratively for each entry. It also implements evasion techniques designed to reduce the likelihood of being blocked or flagged by security systems.
Types of scans performed:
ActiveSync Enumeration — Sends HTTP Basic authentication requests to the Office 365 ActiveSync endpoint. The presence of the X-MailboxGuid header in the response indicates a valid account, even when the supplied password is incorrect.
Autodiscover Enumeration — Issues requests to the Autodiscover endpoint. A 200 status code confirms the account exists, while a 302 redirect suggests the account may not exist.
office.com Enumeration — Interacts with the office.com login page by sending crafted requests. The IfExistsResult field in the response reveals the account status: a value of 0 indicates the account does not exist, while other values confirm the account is present with varying authentication configurations.
Ulteriori Consigli Tecnici
- Account Protection — Enforce multi-factor authentication (MFA) across all users
- Bulk IP Blocking — Access the Fortgale Intelligence Community for up-to-date blocklists
- Disable ActiveSync — Evaluate disabling ActiveSync if it is not actively in use within your organization
- Block Legacy Authentication — Consider blocking legacy authentication methods through Conditional Access Policies (CAP).







