TeamPCP: The Rise of Cloud-Native Extortion and Supply Chain Attacks
TeamPCP is an emerging cybercriminal collective that became active in late 2025, distinguishing itself through a specialized focus on massive attacks against cloud-native infrastructures. Unlike traditional Advanced Persistent Threat (APT) groups that often prioritize deep persistence on specific endpoints, TeamPCP utilizes high-level automation to scale their operations horizontally. They effectively transform compromised cloud environments into functional nodes of a global botnet, which they then leverage for distributed scanning, proxying, and intensive Monero (XMR) cryptomining.
The group’s profile is primarily defined by financial gain. Their revenue streams include direct extortion via data leaks, the theft of sensitive corporate information, and the hijacking of massive computational power. Their targeting is heavily skewed toward exposed cloud surfaces, with internal data suggesting a preference for Azure (61%) and AWS (36%). Consequently, sectors with significant cloud footprints—such as Banking, Fintech, and E-commerce—are at the highest risk.
Evolutionary Tactics: From Worms to Supply Chain Poisoning
TeamPCP’s initial modus operandi relied on automated “worms” designed to traverse the internet in search of misconfigured services or unpatched vulnerabilities. However, their strategy saw a sophisticated shift in early 2026 toward Supply Chain attacks. By compromising popular security and DevOps tools, they have successfully injected malicious code into CI/CD pipelines, allowing them to harvest credentials at the source. The group operates under several known aliases, including DeadCatx3, PCPcat, PersyPCP, and ShellForce.
Chronology of Recent Operations (2025–2026)
The group’s activity peaked during three major campaigns that demonstrated their technical versatility:
- The PCPcat Campaign (December 2025): This operation focused on the low-hanging fruit of the cloud world. The group exploited exposed Docker APIs, misconfigured Kubernetes clusters, unauthenticated Redis instances, and vulnerable Ray dashboards to gain initial footholds.
- The CI/CD Supply Chain Breach (March 2026): In a highly impactful move, TeamPCP compromised security tools such as Aqua Security Trivy and Checkmarx KICS. By injecting malicious logic into official GitHub Actions, they managed to exfiltrate AWS tokens, SSH keys, and Kubernetes secrets from over 10,000 active workflows.
- LiteLLM Poisoning: Recognizing the boom in AI integration, the group poisoned PyPI packages associated with LiteLLM, targeting developers and environments that utilize Large Language Models (LLMs).
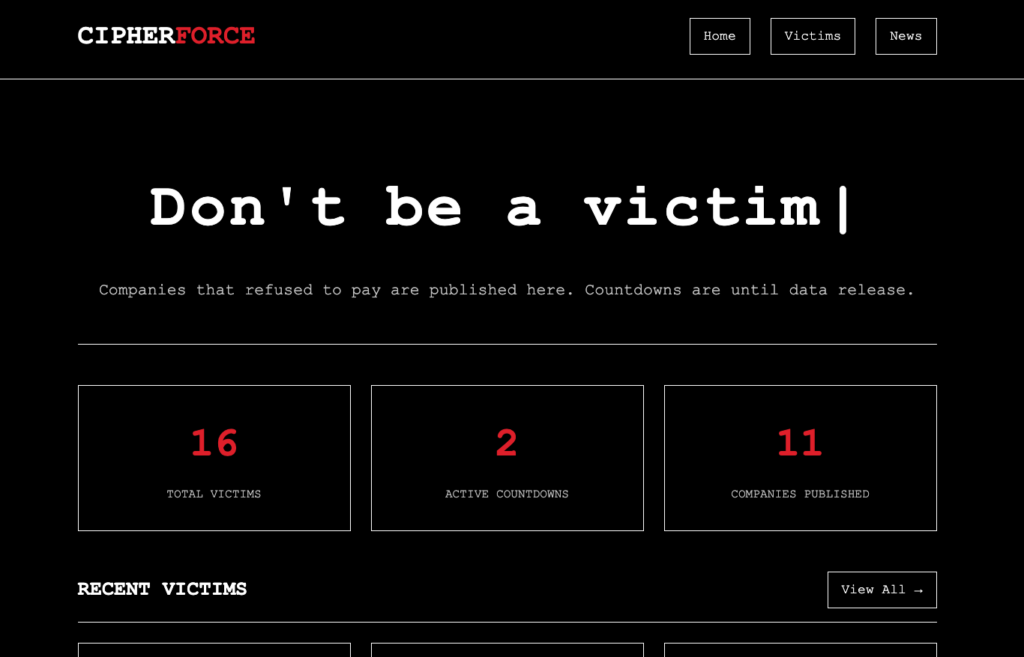
The Onion Data Leak Site (DLS) and Extortion Model
Central to TeamPCP’s financial strategy is their official Onion-based Data Leak Site (DLS). This portal follows the “double extortion” model, where victims are pressured not only to regain access to their systems but also to prevent the public release of their proprietary data.
The portal is designed with a minimalist “cat/shell” aesthetic and features a categorized list of victims. Each entry typically includes a description of the breached entity, the date of the intrusion, and links—often hosted via IPFS (InterPlanetary File System) or public file-sharing providers—to download “proof-of-concept” data. This use of IPFS ensures that even if one gateway is taken down, the stolen data remains redundant and accessible.
Beyond serving as a repository for leaks, the site functions as a communication hub where victims are provided with Tox IDs or encrypted chat links to negotiate ransom payments in private.
Technical Indicators of Compromise (IOCs)
Monitoring for the following indicators is recommended for cloud infrastructure defense:
| Category | Indicator / Value |
| C2 Domains | scan.aquasecurtiy[.]org (Typosquatting), checkmarx[.]zone, models.litellm[.]cloud |
| C2 IP Address | 45.148.10[.]212 (Exfiltration infrastructure) |
| Onion URL | 22evxpggnkyrxpluewqsrv5j4jtde6hut2peq3w44d6ase676qlkoead[.]onion (old)22evxpggnkyrxpluewqsrv5j4jtde6hut2peq3w44d6ase676qlkoead[.]onion (new) |
| Malicious Files | tpcp.tar.gz (Encrypted exfiltration), proxy.sh (Tunneling), kube.py (Lateral movement) |
| Persistence | internal-monitor.service (Systemd service) |
Suspicious Runtime Behaviors:
Observers should watch for the sudden creation of unauthorized Kubernetes DaemonSets or Jobs with names like node-setup-* or host-provisioner-std. Additionally, unexpected outbound traffic from containers toward GitHub or the presence of a repository named tpcp-docs within an organization’s GitHub account are strong signals of active exfiltration.